Hi all,
I am currently working on a Windows 10 machine and WSL2 using Ubuntu 20.04.
I’ve been following the website steps to create my own custom TorizonCore image for an iMX6 using the TorizonCore Extension for Visual Studio Code. I managed to build my Release Container from my Qt5 application. Once built, it is now shown on my Docker Desktop list of images.
Now, to link this to the TorizonCore-Builder tool, I’m understanding that I need to push this image to a Registry. Since I want to keep it private. I’ve been executing the following steps to create a Private Insecure Registry (for now).
On Win10 Powershell
- Pull the registry image:
docker pull registry
- Run local registry container:
docker run -d -p 5000:5000 -v C:/localhub/registry:/var/lib/registry --restart=always --name hub.local registry
- I can see that my registry container is running using
docker ps - Push my image on Docker to my registry:
docker push <laptop's IP address>:5000/my-custom-image
- Confirm my image is in the repository by navigating to 127.0.0.1:5000/v2/_catalog
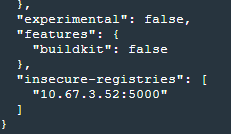
Now that the registry is setup and contains my desired image, I go set it on Docker Desktop as an Insecure Registry like so:
Now I want to go build my image. I will use WSL2 using Ubuntu-20.04 on that same machine. Before calling my Build command with TorizonCore-Builder, I want to call my Bundle command to fetch my image from my Insecure Registry. I’m understanding from the documentation to use a command line similar to the following:
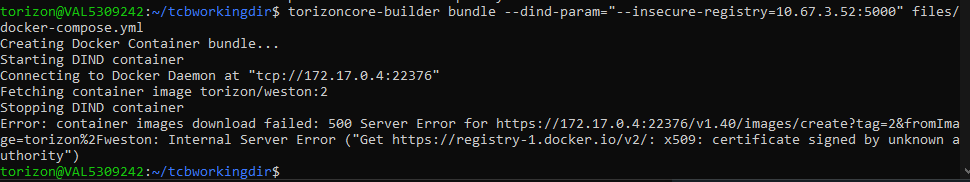
torizoncore-builder bundle --dind-param="--insecure-registry=10.67.3.52:5000" files/docker-compose.yml
The IP matches the machine’s IP as per Windows 10 (ipconfig command) and my docker-compose.yml has been exported from the Dev Container on VSCode as explained in the step-by-step guide:
# docker-compose.yml
services:
my-custom-image:
depends_on:
- weston
device_cgroup_rules:
- c 226:* rmw
devices:
- /dev/ttymxc1
- /dev/ttymxc3
- /dev/fb0
- /dev/mmcblk0p1
- /mnt
- /media
image: my-custom-image
ports: []
volumes:
- /tmp:/tmp:rw
- /dev/dri:/dev/dri:rw
weston:
cap_add:
- CAP_SYS_TTY_CONFIG
device_cgroup_rules:
- c 4:0 rmw
- c 4:7 rmw
- c 13:* rmw
- c 226:* rmw
image: torizon/weston:2
network_mode: host
volumes:
- source: /tmp
target: /tmp
type: bind
- source: /dev
target: /dev
type: bind
- source: /run/udev
target: /run/udev
type: bind
version: '2.4'
Executing the bundle command with these gives me the following output:
I’m not sure what tcp://172.17.0.4:22376 is. I can’t seem to understand why I am getting a certificate error if I am trying to access an Insecure Registry that’s on the same machine. Does anyone have any idea what I’m missing here?
NOTE: I am able to execute docker login/pull commands from WSL2.
Thanks!